Critical infrastructure broadly defined refers to assets or systems that are essential for the functioning of society and the safety and security of a population, and where disruption or destruction of this infrastructure would have a significant impact. This includes a nation’s energy supply, for example, but also its transport network.
That not only makes critical infrastructure a particularly attractive target, it also means an attack has the potential to bring about especially devastating consequences.

Cyber Security in Rail
With increasing digitalisation in every area of society, cyber security is a vital and growing field that companies, infrastructure operators and governments need to embrace. This includes the rail industry.
 Railway-News caught up with Alzbeta Helienek, Lead Systems Engineer at Thales, to talk cyber security in rail, following Thales’s presence as lead co-sponsor at the 2nd Annual Rail Cyber Security Summit that was held in London on 14–15 March.
Railway-News caught up with Alzbeta Helienek, Lead Systems Engineer at Thales, to talk cyber security in rail, following Thales’s presence as lead co-sponsor at the 2nd Annual Rail Cyber Security Summit that was held in London on 14–15 March.
An Accepted Threat
We start by asking her whether rail industry members have all understood and accepted that cyber security is an area that affects them too or whether there is any remaining scepticism. The industry has acknowledged that cyber threats are real, she says. The convincing stage was 5 years ago. She adds that the number of cyber attacks an industry receives every day is in the region of 50,000 – it is constant background noise. So now the rail industry is focused on learning about its vulnerabilities and problems and finding solutions.
Actual Cyber Attacks on our Railways
And there have been real cases where rail systems have been hacked. Ms. Helienek mentions Seoul’s subway system that got hacked over the course of several months in 2014. More than 60 employee computers were infected with malware, resulting in data and information leaks. South Korea accused its neighbour to the north of having been behind the attacks.
In January 2008 a teenager used a modified television remote to hack into a Polish tram system, causing four vehicles to derail. The incident injured twelve people.
In December 2011 hackers attacked a railroad in the Pacific Northwest, disrupting railway signals for two days.
“This is going to sound naïve,” I preface my next question, “but why? What do hackers want?” She’s quick to answer: “blackmail, extortion… they’re professionals, often it’s state-funded”. Ms. Helienek explains, the rail industry is incredibly focused on safety; as a cyber hacking threat, an attack on a safety-relevant feature such as a signalling system is much less likely than an attack on a business-relevant feature. There are major barriers to getting into safety-relevant systems. But attacking a business’s IT infrastructure is an area that’s just more familiar to hackers. They can cause disruption and confusion for economic or political gain. Sometimes, as in the Polish case, it’s a kid messing around. The system’s highly interconnected and a hacker mightn’t even realise the knock-on effects he’s causing in such an interconnected system.
Disruption & Distrust
“Just think of the disruption to a city and its economy,” she says. If the London Underground stopped running, the whole city would come to a standstill with far-reaching consequences for the economy. It would also cause distrust in public transport, the government and the police.
This is true on both counts. The Daily Telegraph reported in January this year on the disruption caused in London as a result of the tube strike with phrases like “swarms of people rushing”, “evacuation […] due to overcrowding”, “chaos”, “endless queues”. And this is for a strike, where we know when it will be, how long it will last and what the motivations are for the people organising it.
The Telegraph article goes on to mention a number of sources attempting to quote figures for just how many millions were lost to the economy as a result; there seems to be agreement at least that that seems something of an impossibility. It does, however, point out an upside to digitalisation. It allows vastly more people to work from home in such an event, reducing its economic impact.
What Are the Most Attractive Targets?
We ask Ms. Helienek whether this suggests that metro systems are much more vulnerable targets than, say, long-distance trains. “You can’t say that,” she tells us. The 2005 attack on the Spanish railway was a long-distance train, the Tokyo gas attack in 1995 was metropolitan. She explains, an attack on a high-speed train for example would be an attack on a prestige project, on one of national pride. It would gain a lot of media attention, which is what hackers are after.
Throughout this conversation Ms. Helienek refers to them as “unpredictable and covert”, as in, you can’t try and guess at what every crazy hacker is trying to do and why – or even where they are operating from. She says it’s the wrong approach. She says the correct response and best protection is to always monitor your systems so you know what’s going on in your network. That way you know what’s normal and when you’re being hacked. The second goal for industry members is to always keep systems moving and operating despite a cyber attack or get systems up and running again as quickly as possible – resilience is key.
 Rail-specific Solutions and Standards
Rail-specific Solutions and Standards
Vigilance and a quick response make intuitive sense of course and that’s exactly what the suppliers and customers at the Rail Cyber Security Summit came to discuss. They need to stay informed on cyber security issues. Ms. Helienek tells us she did attend a multi-industry conference on cyber security three years ago as a lot of the threats they face are the same. But, she says, the solutions are different. The avionics industry or the power industry will have their own processes, solutions and standards. She adds, oftentimes when threats are identified, the response is to do patch management, to close the loophole. In the rail industry it can often take a long time to get approval to make changes when you have to bear in mind the safety protocols and reliability requirements.
Governmental Responses
Okay, so different industries working together is of limited value. But what about governments, I say. Do they respond well? Does she have experience with different governments? Yes, she says. The UK and Austria are really different. As a global city, the threat to London feels more real than it does in a country like Austria – she is Austrian – and therefore it feels like more of a target.
The UK is a more natural, more likely target, she says. It’s part of military operations and it’s a military ally, it’s a member of NATO, unlike Austria. The UK government is aware and prepared and also quick to fund projects and issue guidelines, she adds. Some may say that it is a leader in deploying solutions to tackle cyber threats, however the threat is evolving and so must governments and industry. The new national cyber security strategy says the government will intervene on the grounds of national security if the industry isn’t doing a good job.
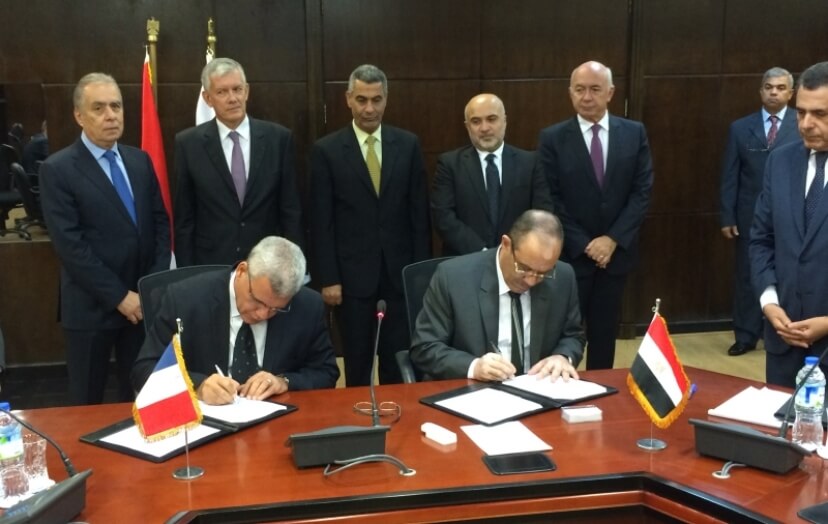
Supranational Approaches: the EU
There are positive initiatives on a supranational level too. The European Union’s Horizon 2020 programme Shift2Rail funds the CYRail project, which was selected by the European Commission to enhance cyber security in the rail industry. CYRail was launched in October 2016 and held its first workshop in Paris in December of that year. It has a project runtime of 24 months and a budget of €1.5 million. The project objectives focus on assessing the most critical railway services and the most innovative attack detection techniques, find counter-measures and mitigation strategies and to determine resilience mechanisms.
Ms. Helienek stresses the importance of standardisation and legal preparedness for the industry. She points us to ETSI, the European Telecommunications Standards Institute, and CENELEC, the European Committee for Electrotechnical Standardization, as two further bodies helping to develop and implement industry-wide standards for cyber security.
What can passengers do?
We take all of this in and feel confident that cyber security in rail is an important topic for industry members, rail authorities, national governments and supranational bodies like the EU. But how about passengers? What can passengers do? Ms. Helienek pauses to think about this one. We’re all familiar with the signs on the London Underground encouraging passengers to report anything suspicious. We know not to leave our luggage unattended because it will be seized and destroyed. The British Transport Police tell us that if we see an unattended bag or package that could be an immediate threat, we should move away and call 999. It’s a very tangible thing. And we know it’s justified. We know about the London 7/7 bombings and the 2004 Madrid train bombings.
So Ms. Helienek says, there needs to be more public awareness, definitely. If passengers see something abnormal, they need to report it, but they need to know what abnormal looks like. Suspicious wifi names or too many open networks for example. She says she wouldn’t be at all surprised to see such an awareness campaign in the near future. Maybe instead of posters warning us about unattended bags, they’ll feature screenshots of suspicious wifi networks.
Ms. Helienek concludes, the railway is not a closed network anymore. It’s interconnected. That opens it up to attacks and allows attacks to have further-reaching consequences, intended or not. Vigilance, preparedness, resilience and rapid response plans will keep passengers safe, companies protected and nations and their critical infrastructure secure.